Windows Password Recovery - DPAPI blob analysis
A DPAPI blob is an opaque binary structure, which contains the application's private data encrypted using DPAPI. Many Windows applications and subsystems store passwords, secrets and private data in DPAPI blobs. To create files with DPAPI blobs (for further analysis), use our DPAPI blob look-up utility.
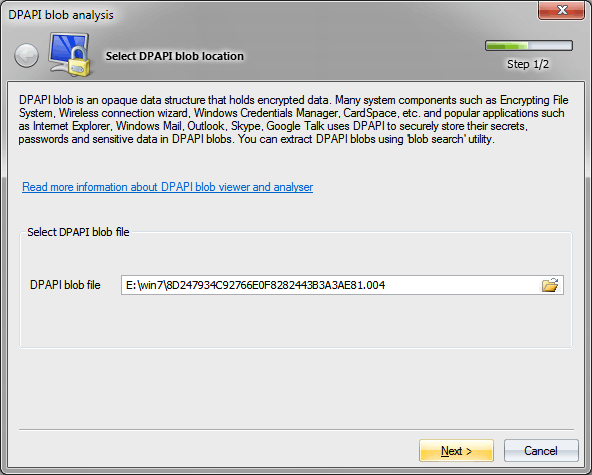
Specify path to DPAPI blob
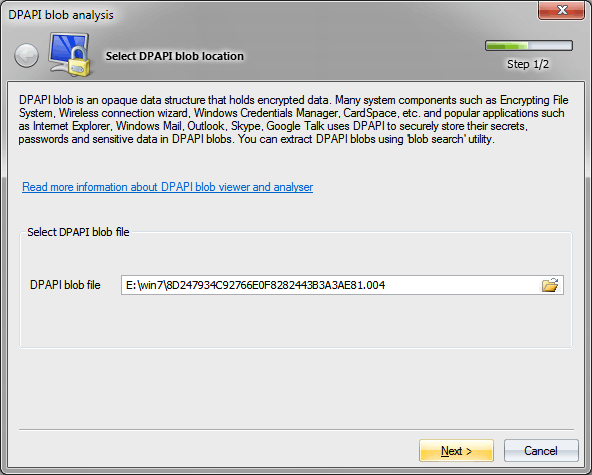
This is the file that was created by the blob search tool.
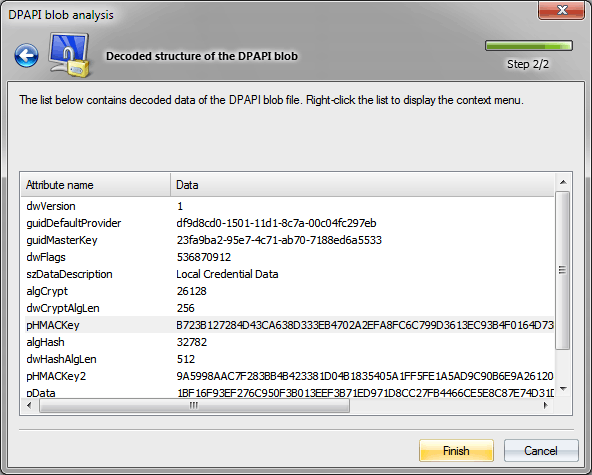
And proceed to analyzing data
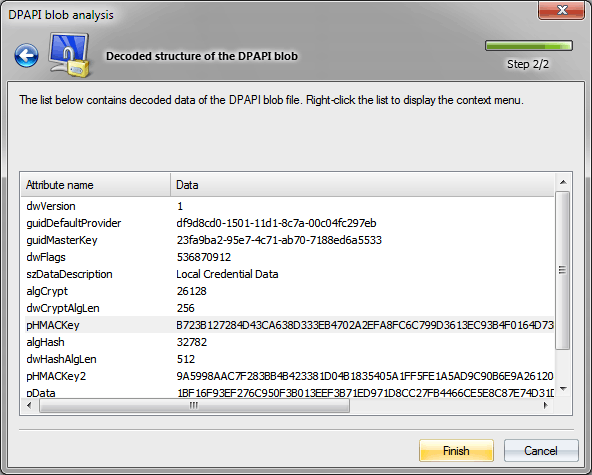
DPAPI blob is a binary data structure, which comprises the following consecutive attributes:
- dwVersion - data structure version. Current data version - 1.
- guidDefaultProvider - data encryption provider, used in encryption function calls, ensures compatibility of versions and organizes simple cryptological primitives. For example, you can set Blowfish or RC5 as a block cipher. Currently, Windows has the following default crypto provider: df9d8cd0-1501-11d1-8c7a-00c04fc297eb, which corresponds with the registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Protect\Providers\df9d8cd0-1501-11d1-8c7a-00c04fc297eb.
- guidMasterKey - Master Key GUID, the data is encrypted with. To decrypt data within a DPAPI blob, first of all you must decrypt the Master Key with the name set in the binary structure guidMasterKey. Only one Master Key can be attached to a DPAPI blob.
- dwFlags - various flags. For example, the bit 3 indicates that the decryption of the data is to be carried out under the SYSTEM account. The bit (dwFlags&0x20000000) seems to be always on. Etc.
- szDataDescription - data descriptor, which is set by the optional parameter LPCWSTR szDataDescr in the function CryptProtectData.
- algCrypt - data encryption algorithm. By default, Windows 7 uses AES 256 (which corresponds to 0х6610 in the hexadecimal or 26128 in the decimal notation), Windows XP - 3DES, Windows 2000 - RC4.
- dwCryptAlgLen - key length in the encryption algorithm.
- pHMACKey - HMAC key 1.
- pSalt - salt (optional).
- algHash - hashing algorithm. By default, Windows 7 uses SHA 512, Windows XP and Windows 2000 - SHA1.
- dwHashAlgLen - hash length in the hashing function.
- pHMACKey2 - HMAC key 2.
- pData - actual encrypted data.
- pSignHash - digital signature for verifying data integrity.