Opera Master Password Recovery screenshots:
choosing Opera Master Password decryption method
During this step, the program's wizard will ask you to choose the decryption method, set the event (notification) to be performed when the password is found, and set a number of additional decryption options.
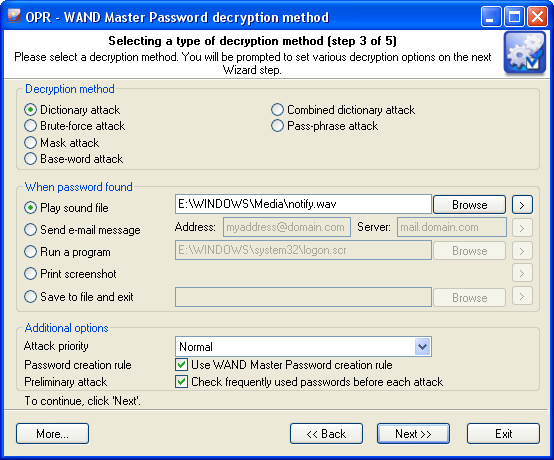
Decryption method
Opera does not store its Master Password in the plaintext format. Moreover, Opera doesn't even store its hash. The developers have chosen a different route: the password along with the salt participates in the encryption of a portion of data and then, to check the validity of the password, it uses the decrypted data hash and the original salt value. This makes it clear, why the calculated tables attack here will be, to put it mildly, not very efficient. The program currently supports several types of decryption of Master Password:
-
Artificial Intelligence Attack is a new type of attack developed in our company. It is based upon a social engineering method and allows, without resort to time-consuming and costly computations, to almost instantly recover certain passwords.
-
Dictionary attack is the most efficient recovery method when the program tries each word from the dictionary (or dictionaries if there are several dictionaries) you specify until it finds the original password or until the wordlist is out of words. This method is very efficient since many people use regular words or phrases for their password. Besides this type of recovery is performed quite fast compared to a brute-force attack, for instance.
-
Brute-force attack. If the dictionary attack has failed, you may need to take a closer look at the brute-force attack, when the program uses all possible combinations from the specified range of characters. For example, for a three-character range of lower-case Latin characters, it will check all possible combinations, starting with 'aaa', 'aab', 'aac', and all the way through 'zzz'. This is the slowest attack, so it is really great for short passwords.
-
Mask attack. This type of attacks is useful if you have at least some information about the password. For example, you may know that the first four characters in the passwords are Latin letters; they are followed by a three-digit number. The mask attack is a variation of the brute-force attack, except that some characters for finding the password remain unchanged, and only a portion of the password may change. The special syntax is used for setting a mask or rule for finding a password. It will be described in detail in the corresponding chapter below.
-
Base-word attack (developed by Passcape). At the first glance, this type of attack reminds the one we just described. It is just as efficient if a portion of the password to be recovered is known to us. However, unlike in the previous attack, here you do not have to set a mask - just provide a basic word. The program will take care of the rest. The phrase attack is based upon the experience of the social engineering and uses over 150 rules for possible modifications of the original phrase to generate a great number of possible password combinations.
-
Combined dictionary attack (developed by Passcape) uses to find compound passwords. It is very similar to the dictionary attack, except that instead of using a single word for password verification it uses a combination of words created by combining words from several dictionaries.
-
Phrase attack (developed by Passcape) is very efficient against complex passwords. The idea of it is to guess the right password by searching through frequently used phrases and combinations.
When password found
This group allows setting an action to be performed automatically when the password is found. This option is convenient, for instance, to system administrators when passwords are being recovered on several computers at once. The program offers five possible notifications: play sound, send e-mail, run application, print screen or store results to file and close the program.
Additional options
In the Additional options group you can specify:
-
Attack priority. If you are planning on using your computer actively during an attack, you are recommended to set the priority value to 'Below normal' or even 'Low'.
-
Password creation rules. You should know that for the creation of its Master Password Opera follows this rule: Master Password must be at least 6 characters long and must consist of numbers and combination of letters. When this option is selected (it is selected by default), the program will ignore passwords that do not comply with this rule.
-
Preliminary attack. The program will check the most frequently used passwords before each attack. Literally, by selecting this option, you activate the fifth type of attack, the preliminary attack. It may take up to 1 minute on slower computers. The preliminary attack consists of three parts and allows to 'catch' short and frequently used passwords like 'qwert1'. The program creates passwords for this attack by following the Master Password Creation Rule.