Recovering domain cached passwords

You can
translate the article into your native language in order to get the program's registration for free.
Intro
Password caching on Windows NT
Setting up caching options
Safety of caching domain passwords
Potential attacks on cached domain passwords
Cached domain passwords - a look from within
Practical guide on recovering user passwords from cached domain entries
Outro
Appendix
Intro
You might have been informed that Windows NT-based operating systems stored or, to be more accurate, cached user passwords on the local machine. That is done in order to allow connecting to the server even when the logon server is not available for some reason. In this case, user will have the access to network resources that do not require the domain validation.
Password caching on Windows NT
Generally speaking, the Windows NT operating systems use two types of password caching:
- General caching
- Domain-level caching
In this case, the latter one is of our interest. Domain-level caching provides at least two functionalities:
- Access to computer resources when domain controller is not available. For example, some laptop user uses a domain account for logging on to the laptop connected to the domain. Then the user moves the laptop to a place where the domain is not available. In such case, Windows would use cached data for logging on to the system locally and ensuring the access to the local resources of the computer.
- Single Sign-On (SSO) - the functionality carries out a one-time network authentication using data obtained during the first interactive sign-on and excluding the reentering of it.
If domain caching is disabled, on an attempt to logon to the server user will get this message:
The system can not log you on now because the domain DOMAIN_NAME is not available
If domain controller is not available, and user data required for the sign-on is stored in cache, the user will get this prompt:
A domain controller for your domain could not be contacted. You have been logged on using cached account information. Changes to your profile since you last logged on may not be available.
Setting up caching options
Number of cached credentialss stored on client side
By editing the registry, one can manually set the required number of preceding logon attempts to be cached by operating system. That value may vary between 0 and 50. If the value is set to 0, caching will be disabled. By default, Windows 'remembers' 10 preceding logons. Caching is controlled with the following registry key:
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\Current Version\Winlogon
ValueName: CachedLogonsCount
Data Type: REG_SZ
Values: 0 - 50
Notifying of logon using cached credentials
If you attempt to connect to domain (using a Windows-based workstation) while the domain controller is unavailable, you will not see any error messages and, therefore, possibly won't notice that have signed on using cached domain.
If you want to configure Windows the way that every time you attempt to sign on using cached password it would show the corresponding warning, set these two registry keys:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft \Windows NT\CurrentVersion\Winlogon
ValueName: ReportControllerMissing
Data Type: REG_SZ
Values: TRUE
And then for each user of the system:
HKEY_CURRENT_USER\Software\Microsoft\WindowsNT\CurrentVersion\Winlogon
ValueName: ReportDC
Data Type: REG_DWORD
Values: 1
Safety of caching domain passwords
The term 'cached domain passwords' doesn't fully reflect the way Windows caches and stores private information. Beginning with Windows 2000, user name and passwords are not stored in the open format. On the contrary, the system stores password hash, slightly modified with salt (i.e. salted hash), which in its turn is generated on the basis of user name in the Unicode format.
If a potential hacker attempts to carry out the simplest cryptanalysis, as Microsoft claims, the following conclusions can be drawn from this encryption algorithm:
- Precompiled tables must be generated for each salt
- Hash cannot be used for signing on to other systems
Approaching this issue from the other point may reveal that:
- Precompiled tables can be created for aliases, i.e. for known user names; e.g., for the built-in administrator or guest. On the other hand, this may turn out to be wasted time, since cached credentials of built-in administrators, to say it polite, aren't frequent in occurrence.
- To completely eliminate the possibility of signing on to other systems, along with user name one should also salt domain name.
Potential attacks on cached domain passwords
A potential malefactor, to gain the access to the computer, can add a new or overwrite the hash with his own value. The procedure assumes the physical access to the computer.
However, the mere rewriting or replacement of a cached password doesn't give the potential malefactor the access to other users' data, Encrypting File System, private data encrypted with DPAPI (e.g., IE, Outlook, Windows Mail, WPA and other passwords).
Cached domain passwords - a look from within
Cached domain records are stored encrypted in Windows registry, in the branch HKEY_LOCAL_MACHINE\SECURITY\Cache. The binary value with the name NL$х indicate one cached record, where 'х' stands for the record number. The access to this branch of the registry is granted to the system only.
Each record contains:
- Extended information on the user. Namely: user's short and full name, time of the last access, identifier in the system, domain name, domain DNS name, sign-on domain, script, path to user profile, home directory, home directory drive, membership in groups, etc.
- Private information, including password hash, additional secrets and iteration counter Pbkdf2 (for Windows Vista and, possibly, later operating systems).
The encryption of cached domain records involves the LSA secret NL$KM, which stores the 64-byte Master Key bound to the local computer. NL$KM is located in the SECURITY registry file and, in its turn, is also encrypted with SYSKEY.
Thus, the overall domain record decryption scheme looks this way:
- SYSKEY + LSA Master Key + NL$KM = DCP Master Key
- DCP Master Key + NL$x entry = Decrypted DCP entry
After we have decrypted the cached domain entry, we gain the access to the user hash.
Briefly, the password encryption algorithm can be described this way.
For Windows 2000-2003: hash = MD4 ( MD4(user password) + lowercase(user name) )
Beginning with Windows Vista, the password wrap-up algorithm has changed a bit. Now it's stuck in a multi-thousand cycle, and the search speed should be lower than even with WPA-PSK:
hash = PBKDF2_SHA( MD4 (MD4(user password)+lowercase(user name)), iterations )
By default, the iterations value is equal to 10240. Please note that the number of SHA passes will be several times greater than this value.
Practical guide on recovering user passwords from cached domain entries
The only tool we will need to get the job done is Network Password Recovery Wizard; its latest version acquired the support of cached record recovery. Let's split the entire assignment into three pieces:
- Decryption of cached domain entries
- Analysis of obtained data
- Decryption of password for selected entry
So, let's get going.
1. Decryption of cached domain entries
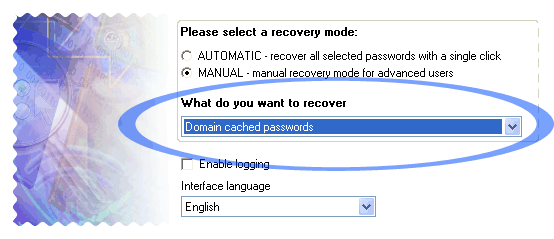
Launch the application and from the drop-down menu select what we want to recover: Domain Cached Passwords. If the cached records are on the local computer, with confidence fire up the automatic mode and move ahead.
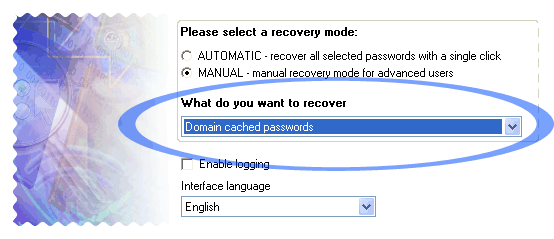
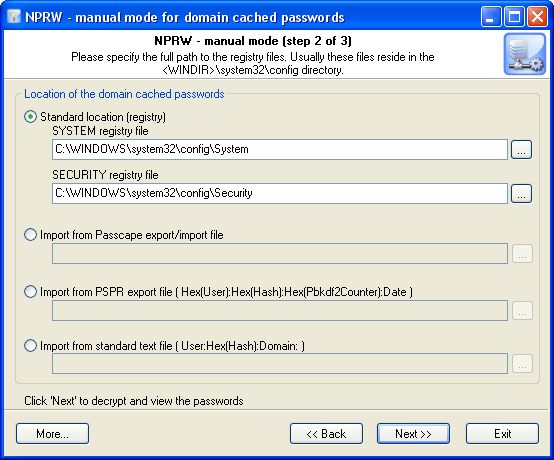
The manual operating mode is more flexible and allows user to manually select data source, whether that's the standard location (registry files), Passcape's native import/export file or imported from a file used in other programs.
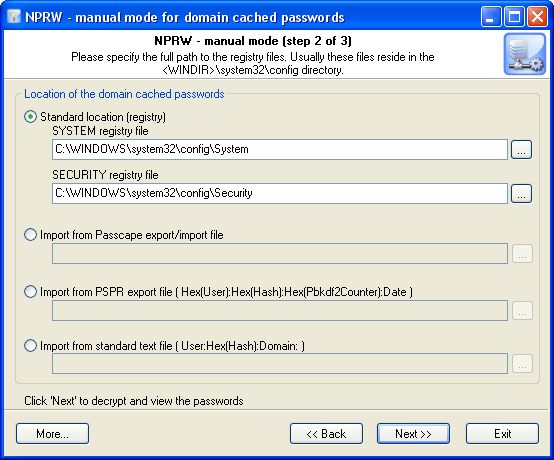
Click 'Next' and wait for the calculation results.
2. Analysis of obtained data
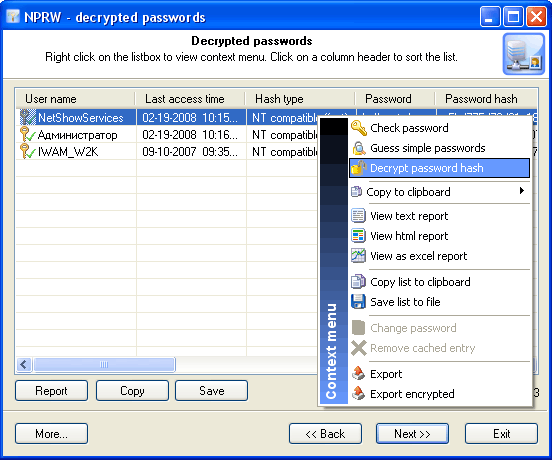
Upon a successful decryption or import of the data, the user will be offered a list of decrypted records. Each record has several fields; for instance, user name, server, membership in groups, etc.
Opening up the context menu by right-clicking allows engaging the program's extended capabilities. For the entire list: copy, save, view report or export entire list. For an individual record: change password, delete record, validate password, recover password by searching the simplest, frequently occurring combinations, or launch a full-scale attack.
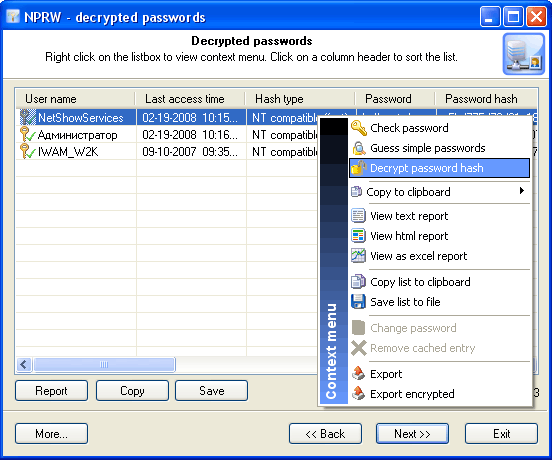
Before launching the attack on password of the selected record, take a note of these two fields: 'Password' and 'Hash type'. Sometimes a cached password can be recovered without appealing to the full attack. In such case, if the program has found the password of the record, it will be kept in the 'Password' field, and the record will be marked with the corresponding icon.
The 'Hash type' field contains password hash type, which can be 'NT compatible instant' - instant recovery, 'Win2K compatible fast' - quick recovery at the speed of several millions of passwords per second or 'Vista, slow' - the recovery speed is only several hundreds of passwords per second on a modern computer.
3. Decryption of password for selected entry
So, to begin the recovery of the password for a selected record, right-click on it and then select 'Decrypt password hash' on the context menu. This will open up the decryption method selection dialog, common to all Passcape Software programs. There is no sense in describing all types of attacks; the detailed information on that can be found on the pages related to the recovery of Opera passwords or Firefox Master Password.
Unsophisticated user might ask a completely reasonable and coherent question: "There is no 100% guarantee of the recovery, although there are many methods; which attack should I start with to raise the probability of its successful completion?"
For choosing the type and the sequence of the attacks, we advise to follow this algorithm, which is applicable in the majority of cases to all types of passwords to be recovered:
- First, enable the preliminary attack option, if it is available. It will help to recover simple and frequently occurring combinations.
- Second, if you are aware of any specifics of the password you are looking for, it's better to try mask attack or base-word attack first. Specifically, if you know a part of the password - using mask attack would be more effective. If you know the basic component of the password or, for example, know the password but don't remember the sequence of caps and lowercase characters in it, base-word attack would do the job better.
If you have no information on the password you are looking for, which occurs most frequently, be guided by the following sequence of steps:
- Run AI attack with mutation and indexing options set to light.
- If the password was not found, just try again and set mutation option to 'normal' level and indexing to 'deep'.
- Launch dictionary attack with the mutation option disabled.
- Launch dictionary attack with the mutation option enabled; the depth of mutation depends on the amount of available time and the attack speed. When searching for passwords typed in the national keyboard layout, the depth of mutation should be set to strong.
- Select and download online dictionaries and repeat steps 3 - 4.
- Launch pass-phrase attack with the mutation option disabled.
- Launch pass-phrase attack with the mutation option enabled and set to the maximum productivity. This will allow finding passwords typed in the national keyboard layout.
- Select and download online pass-phrase dictionaries and repeat steps 6 - 7.
- Launch combined dictionary attack with defined phrase generation rules.
- Select and download online dictionaries for combined attack and repeat step 9.
- Select a charset for brute-force attack, launch the attack.
- If necessary, select a new or complete the old character set and repeat the brute-force attack; i.e. step 11.
Steps 1-2 - Scan your local system for the lost password.
Steps 3-5 - Finding single-word passwords.
Steps 6-10 - Finding multiple-word passwords.
Steps 11-12 - Exhaustive search.
Conclusion
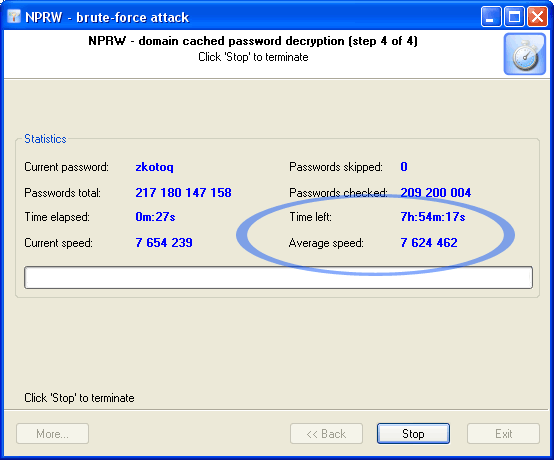
Certainly, if the attack speed makes up millions of passwords per second, like with Windows 2000-compatible domain passwords (remember the field 'Hash type' on the list of cached entries?), you can take advantage of all kinds of attack in full. However, when searching Windows Vista hashes, at the speed of just a couple of hundreds of passwords per second, it's difficult to count seriously on anything but dictionary attack.
Let's take a look at an example and see how long it will take to carry out an exhaustive search attack and recover a simplest, eight-character password in the both cases. Thus, to search through the entire range of characters a..z, we would need to validate not too many and not too few but exactly 217 180 147 158 passwords.
Now, let's look at the timings.
Recovering Windows 2000, XP, 2003 domain cached passwords
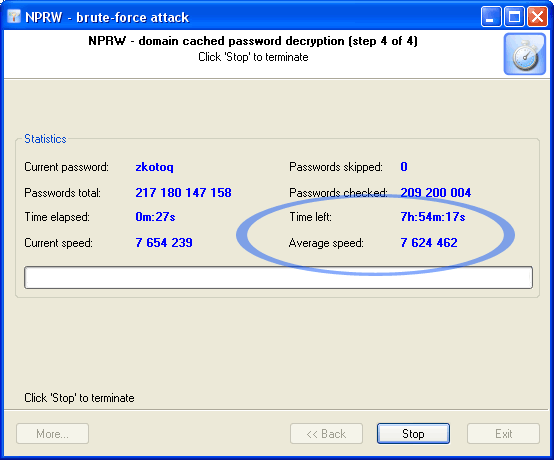
Recovering Windows Vista domain cached passwords

The conclusions, we suppose, are made already.
Appendix
Algorithm for validating cached record password hash in Windows 2000, XP, 2003:
BOOL CheckCachedDomainPassword(LPCTSTR cszUserName, LPCTSTR cszPassword, BYTE pCheckHash[0x10])
{
WCHAR wsz[256];
BYTE pHash[0x10];
INT iLen;
iLen=strlen(cszPassword);
MultiByteToWideChar(CP_ACP,MB_PRECOMPOSED,cszPassword,iLen,wsz,256);
Md4Init();
Md4Update((LPBYTE)wsz,iLen*2);
Md4Final(pHash);
iLen=strlen(cszUserName);
MultiByteToWideChar(CP_ACP,MB_PRECOMPOSED,cszUserName,iLen,wsz,256);
CharLowerW(wsz);
Md4Init();
Md4Update(pHash,0x10);
Md4Update((LPBYTE)wsz,iLen*2);
Md4Final(pHash);
return ( memcmp(pCheckHash,pHash,0x10)==0 );
}
Read more about Network Password Recovery Wizard
This document may be freely distributed or reproduced provided that the
reference to the original article is placed on each copy of this document.
(c) 2008 Passcape Software. All rights reserved.